ot-unlock-luks tool
You have to read, understand and accept the disclaimer .
You are using ot-unlock-luks at your own risk! There is no guarantee - neither implicitly nor explicitly - given, that using ot-unlock-luks wont affect your system in some negative way.
You are allowed to use ot-unlock-luks to recover access to your personal linux-installation. Commercial use, or using ot-unlock-luks to unlock user-accounts of third-party persons or organizations is explicitly prohibited.
Trying to gain illegal access to third-party computer systems is a serious crime in several countries.
About ot-unlock-luks
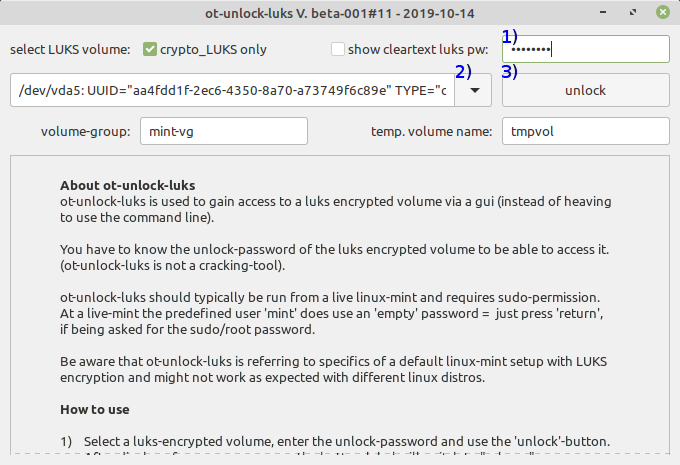
ot-unlock-luks is used to gain access to a luks encrypted volume via a GUI (instead of heaving to use the command line).
You have to know the unlock-password of the luks encrypted volume to be able to access it. (ot-unlock-luks is not a cracking-tool).
ot-unlock-luks should typically be run from a live linux-mint and requires sudo-permission. At a live-mint the predefined user ' mint ' does use an 'empty' password = just press 'return', if being asked for the sudo/root password.
Be aware that ot-unlock-luks is referring to specifics of a default linux-mint setup with LUKS encryption and might not work as expected with different linux distros.
Download and run
Download ot-unlock-luks and run it using the preinstalled python - python 2 or python 3 should work both - python3 setups are typically more up-to-date.
Copy/paste the following to a terminal (right-click at the terminal should offer an paste-entry):
# open a terminal and run cd ~/Downloads wget https://www.orcus.de/Entities/linux/ot-unlock-luks-001.py --backups=1 python3 ot-unlock-luks-001.py
If you are not using linux mint or wget is not available for some reason use curl instead:
# open a terminal and run cd ~/Downloads curl -O https://www.orcus.de/Entities/linux/ot-unlock-luks-001.py python3 ot-unlock-luks-001.py
If ot-unlock-luks is run without root-rights, it offers to reload itself using sudo-credentials. At a live-mint , the predefined user ' mint ' does use an empty password, press the 'return'-key ('enter'-key) if being asked for a password.
How to use
1) Enter the unlock-password.
If you are using a foreign keyboad layout, you might activate the option show cleartext luks pw , to display the entered password.
2) Select a luks-encrypted volume.
The default selection is filtered, to show only volumes having an entry TYPE=crypto_LUKS . To display all available volumes: Uncheck the option crypto_LUKS only .
3) Use the 'unlock'-button.
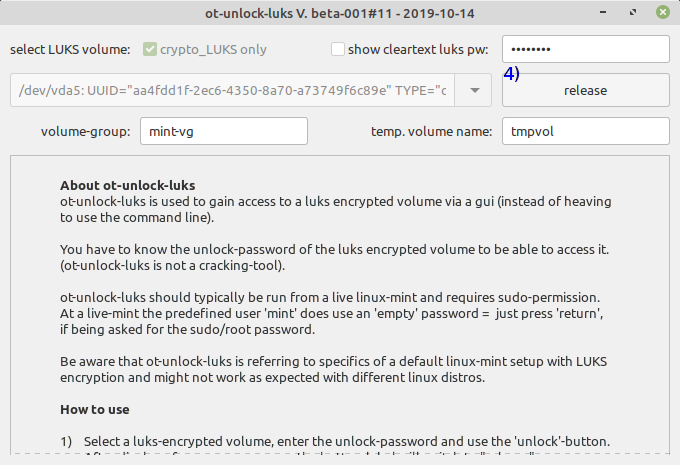
After display of a success-message, the button-label will switch to release .
Keep ot-unlock-luks running and switch to the file manager, which should offer the decrypted volume now and mount it this way.
When you are done with the decrypted volume, unmount it, using the file manager, before switching back to ot-unlock-luks.
4) Use the button release at ot-unlock-luks to finally close the luks-encrypted volume.
After display of a success-message, the button-label will switch back to unlock .
You can close ot-unlock-luks now.
Trouble-shooting
1) Empty volume list
Available volumes are initially filtered to show only volumes with an field TYPE="crypto_LUKS . If you are using a volume with a different TYPE-field: Uncheck the option crypto_LUKS-only , to show all available entries.
2) Does not unlock volume
After entering the unlock-password and using the button unlock , the button-label does not change (still showing unlock ) = the volume cant be unlocked:
You either did select a volume, which does not offer a supported filesystem, or the used password has been invalid. In rare cases a filesystem-error might prevent access.
Select the 'correct' volume and double check your password. Especially if you are not using a EN-US keyboard layout: turn on the option show cleartext luks pw and check the used luks password.
Broken filesystems cant be accessed without repair. If you suspect a filesystem-error, you might want to check for the output of dmesg at a terminal.
3) Upps - did close ot-unlock-luks before unmounting the volume
Just run ot-unlock-luks again and use the unlock-button (it will ignore that the volume is already unlocked). Afterwards you should be able to release the volume as intended.
test - coverage
Internally tested linux versions are (using an almost default-setup, fully updated):
- mint 19.2 64 bit
Known issues
-- None --
